KDP publishers find profitable niches by following a comprehensive research and validation process, focusing on identifying a broad niche, refining it into a sub-niche, and

The world of casino slots has changed dramatically in recent years, with a huge number of games now available from diverse providers. With so many

“Atomic Habits” by James Clear offers a comprehensive guide on habit formation and improvement, emphasizing the power of small, incremental changes. Clear introduces a practical

In the colorful world of online slot gaming, themes come in all shapes and sizes, but few capture the imagination quite like pig-themed new no

In the ever-evolving realm of gambling, online casinos such as Free Bet Casino have marked a significant paradigm shift, posing challenges and opportunities for their

MrBeast, a well-known figure on YouTube, masterfully employs psychological tactics to draw viewers into his content. Inhis videos, he frequently leverages Input Bias, Costly Signaling,

Publishers can significantly increase the value of an individual book by employing various strategies that expand its reach, lifespan, and revenue potential. We’ll take a

“Blitzscaling” by Reid Hoffman outlines the strategy of prioritizing speed over efficiency in the face of uncertainty to achieve rapid growth and first-mover advantage. Here

Among the many use cases for LLMs (e.g., ChatGPT, Claude, Google Gemini), they can disrupt conventional thinking patterns to help you think more creatively and

If your phone won’t charge, here are some steps and considerations that might help troubleshoot and potentially solve the problem. Tips Summary If Phone Won’t

Facebook remains a potent channel for driving website traffic. However, leveraging this platform effectively requires a nuanced approach, blending creativity with analytics. Here’s a guide

In publishing and content creation, writers are increasingly looking beyond traditional book sales to build diversified, resilient businesses. By leveraging their content, expertise, and personal

Navigating personal finance can often lead us to seek advice from the most accessible sources: our family and friends. While their insights are usually offered

Here’s a list of 15+ of the best travel movies to inspire your wanderlust: Into the Wild (2007) Based on a true story, a young

Here’s a selection of basketball movies worth checking out: Hustle (2022) Adam Sandler stars as a washed-up basketball scout who discovers a raw talent overseas
When it comes to the best price for a book, finding the sweet spot involves balancing several factors, including: Genre Nonfiction: Nonfiction titles often command higher

Are you looking for how to type the Backwards 3 “Ɛ” symbol? We have a step-by-step guide on how to use the backward 3 (aka
Here’s a breakdown of sites similar to Seeking Alpha that pay contributors for their investment and financial analysis articles: Top Direct Competitors The Motley Fool:
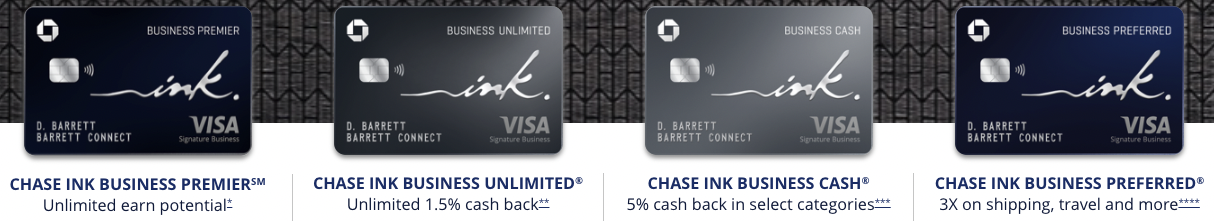
Chase offers a range of business credit cards catering to different needs. In this comparison, we will detail the specific features and benefits of the:
J.K. Rowling’s journey with the Harry Potter series spanned well over a decade, from the initial idea to the publication of the final book. Here’s